British Airways Penalty Notice: the download
The ICO’s landmark decision is a worthwhile read, but for those who don't have time to tackle all 144-pages, Bryony Couchman has summarised the key points below
Background
On 16 October 2020, the ICO concluded its investigation into the British Airways 2018 data breach and imposed a fine of £20m. Given the ICO's dramatic departure from the massive £183.39m fine proposed last year, and as is clear from its 144-page Penalty Notice, the ICO was adamant to get it right this time.
Given the landmark nature of the decision, the Penalty Notice remains a worthwhile read, but for those who don't have time to tackle all 144-pages, we have summarised the key points below.
The Attack
Between 22 June and 5 September 2018, BA's systems were hacked and the attacker accessed payment card and personal data of approximately 429,000 customers, and username/passwords for a further 612 customers across the globe.
The attacker initially gained access to a remote BA network using login details provided by BA to Swissport, a third-party supplier of cargo services. The attacker was then able to use the compromised Swissport account to "breakout" of the remote network into the wider BA network. We've written previously about the significance of third-party and outsourcing risk (see here).
The attacker obtained customers' names, addresses, payment card numbers and CVV codes via two methods: (1) unencrypted log files on BA's systems; and (2) redirecting payment card details from the BA website to a site controlled by the attacker.
On 5 September 2018, a third-party informed BA that data was being sent from its website to an external website. BA identified and contained the hack the same day.
On 6 September 2018, BA notified the ICO and the affected customers, notifying further customers the following day.
Procedure
On 8 July 2019, the ICO confirmed its intention to fine BA £183.39m under GDPR in relation to the breach. Between 5 September 2019 and 2 July 2020, BA provided three detailed sets of written representations and various responses to requests for further information to the ICO. BA did not admit liability and argued that the ICO had applied an incorrect standard to the relevant Articles of the GDPR. BA's non-admission of liability is important in light of the class action proceedings underway in relation to this breach. Follow on actions are an increasingly significant part of data breach risk (see our recent articles here and here).
Whilst the opportunity to make further representations was not required by law, the ICO permitted BA's request to make its second representations given (i) the complexity of the case, (ii) BA's existing representations, and (iii) the fact that this was one of the first major decisions made under the new EU data protection regime. In return, BA agreed to a statutory extension of time for the issuing of the decision.
BA's third representations, together with oral submissions, were made in response to the ICO's request for information regarding the financial impact on BA of the COVID-19 pandemic.
The ICO's decision
1. BA's failures
The ICO found that BA failed to comply with its obligations under Article 5(1)(f) and Article 32 GDPR because it failed to put in place appropriate technical or organisational measures to protect personal data.
The ICO found that each step of the attack could have been prevented, or its impact mitigated, by BA implementing measures that were open to it. For example:
BA could have used measures such as Multi-Factor Authentication (MFA), external public IP address whitelisting, and IPSec VPN, in order to mitigate the risk of an attacker being able to access the BA network by compromising a single username and password (notably, the ICO found that BA could not rely on the security standards it had set for its suppliers alone as an effective security measure).
BA did not have an up-to-date risk assessment for its Citrix remote access gateway, meaning it had not taken steps to mitigate the risk of the attacker "breaking out" of the gateway and gaining access to the wider network.
BA had several features/tools freely available as part of the Microsoft Operating System which would have permitted early detection so that BA could have detected and removed the attacker before privileged accounts were compromised.
2. Rejection of BA's wider arguments
The ICO rejected BA's argument that the ICO had misapplied Article 25 GDPR because it was not in force at the time BA designed the relevant data processing systems, finding that it applies "at the time of the processing itself" as well as at the point at which the system is designed. Nonetheless, the ICO decided not to make a finding under this article in the final decision.
The ICO rejected BA's suggestion that the airline industry should not be subjected to the same security standards as other industries.
The attack was not of such a degree of sophistication to negate BA's responsibilities for securing its systems. The ICO did not find that simply because an attack took place BA was in breach of its obligations, the attack instead exposed BA's security failures.
3. Calculation of the fine
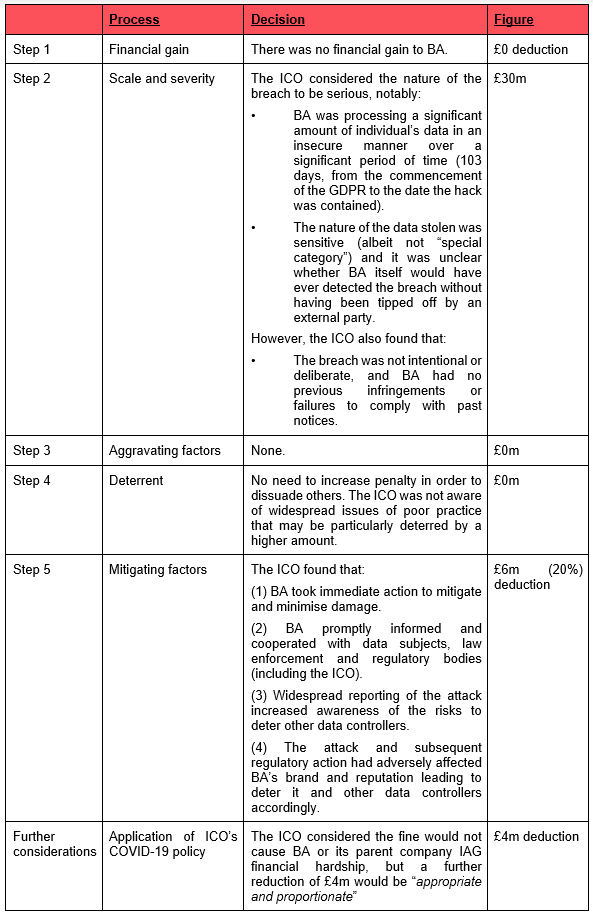
The ICO applied the five-step process outlined in its Regulatory Action Policy to calculate the fine:
Despite the ICO's extensive commentary on its calculation, the decision raises more questions than it does answers. Part 2 of our series on the Penalty Notice, titled "British Airways penalty - Reduction or Reformulation?", will attempt to answer the biggest of these questions: should firms' expectations as to the scale of ICO fines be revised downward as a result of BA's experience?
If you found this interesting, there's a lot more comment you may find helpful on UpData, which provides regular updates on contentious, criminal and insurance risks relating to data, from cyber-attacks to regulatory enforcement.

.jpg?crop=300,495&format=webply&auto=webp)
_11zon.jpg?crop=300,495&format=webply&auto=webp)







.jpg?crop=300,495&format=webply&auto=webp)




